AI in Cybersecurity: Revolutionizing Threat Detection & Defense

Introduction
In an increasingly interconnected world, the digital landscape is both a source of immense opportunity and a battleground for sophisticated cyber threats. Traditional cybersecurity measures, while foundational, often struggle to keep pace with the sheer volume, velocity, and complexity of modern attacks. This is where the power of Artificial Intelligence (AI) and Machine Learning (ML) steps in, ushering in a new era of proactive and robust defense. The integration of AI in cybersecurity isn’t merely an upgrade; it’s a paradigm shift, revolutionizing how organizations approach AI threat detection and AI for cyber defense.
From identifying subtle anomalies that hint at an impending breach to orchestrating rapid, automated responses, cybersecurity AI is transforming every facet of digital protection. This article will delve deep into how AI is becoming an indispensable ally in the fight against cybercrime. We’ll explore the cutting-edge ways machine learning cybersecurity enhances threat intelligence, automates routine tasks, and empowers human analysts to focus on high-stakes strategic defense. Join us as we uncover the innovative AI security solutions defining the future of cybersecurity AI and charting a course towards a more secure digital future.
The Evolving Cyber Threat Landscape: Why Traditional Methods Fall Short
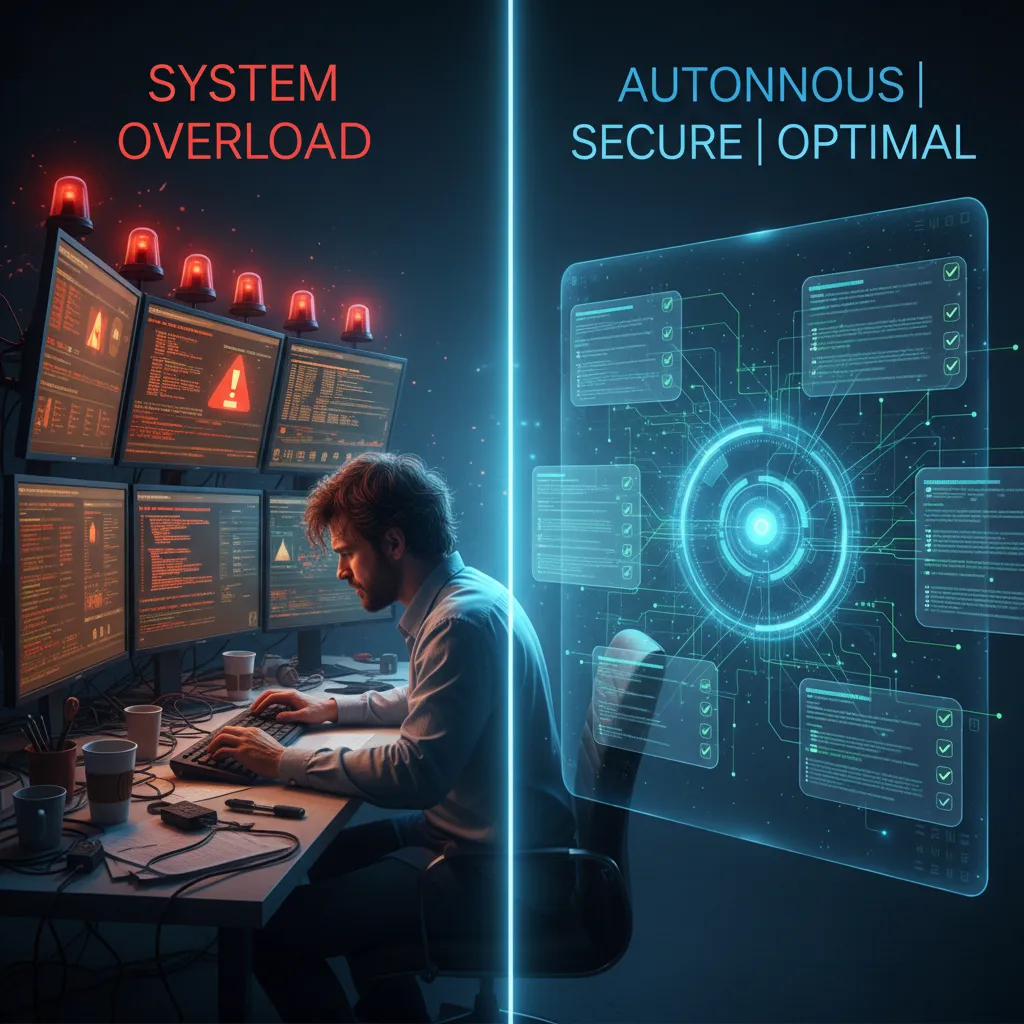
The digital world is under constant siege. Cybercriminals are more organized, resourceful, and technically adept than ever before. We’re witnessing an exponential rise in advanced persistent threats (APTs), polymorphic malware, sophisticated phishing campaigns, and zero-day exploits. Traditional, signature-based detection systems, while effective against known threats, are often outmaneuvered by novel attacks that exhibit slight variations or entirely new attack vectors.
Manual analysis of security logs and alerts is humanly impossible given the sheer volume of data generated by modern networks. Security Operations Centers (SOCs) are often overwhelmed, leading to alert fatigue, missed threats, and delayed incident responses. This reactive stance leaves organizations vulnerable, highlighting the urgent need for more intelligent, adaptive, and proactive defense mechanisms. This is precisely where the capabilities of cybersecurity AI prove transformative, providing the necessary agility and insight to stay ahead of adversaries.
AI Threat Detection: Spotting the Unseen
At the heart of AI’s revolution in cybersecurity lies its unparalleled ability in AI threat detection. Unlike traditional systems that look for pre-defined patterns, AI and machine learning algorithms can analyze vast datasets to identify anomalies, predict potential threats, and even uncover entirely new attack techniques.
Behavioral Analytics and Anomaly Detection
One of the most powerful applications of AI behavioral analytics in cybersecurity is its capacity to establish a “baseline” of normal network and user behavior. By continuously monitoring user activities, network traffic, and system logs, AI can learn what constitutes legitimate operation. Any deviation from this baseline—a user accessing unusual files, a device connecting to suspicious external IPs, or a sudden surge in data transfer—triggers an alert.
This approach is crucial for detecting zero-day attacks, insider threats, and advanced malware that might bypass signature-based detection. For instance, AI network security systems can analyze packet headers, traffic patterns, and communication protocols to identify botnet activity or data exfiltration attempts in real-time. Similarly, AI endpoint security leverages behavioral analysis to monitor processes, file access, and registry changes on individual devices, flagging malicious activities before they can cause widespread damage.
AI Malware Detection and Classification
The sheer volume of new malware variants released daily makes manual analysis and signature updates a losing battle. AI malware detection employs machine learning models to analyze various characteristics of executables, such as code structure, API calls, and behavioral patterns during execution in sandboxed environments.
- Signatureless Detection: AI can identify malicious software even if its signature isn’t in a database, by recognizing its inherent malicious traits.
- Polymorphic and Metamorphic Malware: AI algorithms are particularly adept at detecting these evolving threats, which constantly change their code to evade detection.
- Ransomware Identification: By monitoring file encryption processes and access patterns, AI can often detect ransomware attacks in their early stages, allowing for quick isolation and mitigation.
[Related: supercharge-your-content-top-ai-tools-for-creators-in-2024]
Predictive Cybersecurity AI: Anticipating the Next Attack
Beyond detection, AI offers remarkable capabilities in prediction. Predictive cybersecurity AI leverages historical data, threat intelligence feeds, and global attack patterns to forecast where and how the next attacks might occur. This allows organizations to move from a reactive to a truly proactive defense posture.
- Vulnerability Management AI: AI can analyze vast amounts of vulnerability data, identify weak points in an organization’s infrastructure, and prioritize patching efforts based on the likelihood of exploitation. It can predict which vulnerabilities are most likely to be targeted by specific threat actors.
- Threat Intelligence: AI continuously sifts through open-source intelligence (OSINT), dark web forums, and proprietary data to identify emerging threats, new attack methodologies, and adversary tactics, techniques, and procedures (TTPs). This AI security intelligence provides actionable insights for strengthening defenses.

AI for Cyber Defense: Automated Responses and Enhanced Security Operations
The true power of AI for cyber defense extends beyond mere detection into automated response and optimization of security operations. This not only enhances effectiveness but also significantly reduces the burden on human security teams.
Automated Threat Response and Incident Management
One of the most critical advancements brought by AI is the ability to enable automated threat response. When an AI system detects a credible threat, it can initiate pre-defined actions without human intervention, dramatically reducing the “dwell time” of an attacker within a network.
- Network Isolation: Automatically quarantining compromised devices or segments of the network.
- Blocking Malicious IPs/URLs: Updating firewalls and intrusion prevention systems to block known threat indicators.
- Credential Revocation: Automatically resetting passwords for accounts showing suspicious activity.
- Security Orchestration, Automation, and Response (SOAR): AI-powered SOAR platforms integrate various security tools and workflows, automating repetitive tasks, enriching alerts with context, and guiding human analysts through complex incident response playbooks. This leads to faster, more consistent incident resolution and enhanced AI incident response.
AI-Powered Security Operations and Analytics
The modern Security Operations Center (SOC) faces a deluge of alerts and data points daily. AI powered security operations revolutionize how SOCs function by providing sophisticated AI security analytics.
- Alert Prioritization: AI can analyze the context, severity, and potential impact of alerts, prioritizing the most critical ones for human review, thus combating alert fatigue.
- Root Cause Analysis: AI can correlate events across different security tools and data sources to quickly identify the root cause of an incident, accelerating investigation times.
- Threat Hunting: AI assists threat hunters by identifying subtle patterns and anomalous behaviors that might indicate an ongoing, undetected attack, making proactive cyber defense a reality.
- Security Posture Management: AI continuously assesses an organization’s security posture, identifying misconfigurations, compliance gaps, and areas for improvement, helping to build a truly next-gen cyber defense.
Enhancing Specific Security Domains with AI
AI’s versatility allows its application across various specialized cybersecurity domains:
AI Fraud Detection
Financial institutions and e-commerce platforms heavily rely on AI fraud detection to identify unusual transaction patterns, account takeover attempts, and synthetic identities. AI models can process billions of transactions, flagging anomalies in real-time that human analysts would miss. This protects both businesses and consumers from financial losses.
Cloud Security AI
As more organizations migrate to the cloud, securing these dynamic and distributed environments becomes paramount. Cloud security AI helps monitor cloud infrastructure for misconfigurations, unauthorized access, and anomalous traffic patterns across IaaS, PaaS, and SaaS layers. It automates compliance checks and ensures adherence to security policies in dynamic cloud environments.
Data Protection AI
Protecting sensitive data is a core cybersecurity challenge. Data protection AI can classify data, monitor its movement, and detect unauthorized access or exfiltration attempts. It can also help enforce data loss prevention (DLP) policies by identifying and encrypting sensitive information automatically.
AI for Phishing Detection
Phishing remains one of the most common and effective attack vectors. AI for phishing detection analyzes email content, sender reputation, embedded URLs, and attachment metadata to identify and block malicious emails before they reach end-users. It can even detect highly sophisticated spear-phishing attempts that mimic legitimate communications.
Zero-Trust AI
The zero-trust AI model shifts from “trust but verify” to “never trust, always verify.” AI plays a critical role in continuously authenticating users and devices, assessing their posture, and enforcing granular access controls based on real-time risk assessments. This ensures that only authorized entities with appropriate privileges can access specific resources, regardless of their location.
The Synergy of Human and AI: A Collaborative Future
While AI offers immense capabilities, it’s crucial to understand that it is not a silver bullet, nor is it intended to fully replace human expertise. Instead, the most effective AI security solutions foster a powerful synergy between human intelligence and artificial intelligence.
Human analysts bring critical thinking, intuition, contextual understanding, and the ability to adapt to truly novel, unforeseen scenarios—qualities that AI currently lacks. AI, in turn, handles the drudgery of data analysis, alert correlation, and automated responses, freeing up human talent to focus on strategic planning, complex investigations, and proactive threat hunting. This collaborative approach leads to more robust and resilient proactive cyber defense.

Challenges and Ethical Considerations in AI Cybersecurity
Despite its transformative potential, the deployment of ethical AI cybersecurity solutions comes with its own set of challenges and considerations.
Adversarial AI
A growing concern is the rise of adversarial AI, where attackers use AI to bypass AI defenses. This includes crafting “evasion attacks” that subtly alter malware to trick AI detection models or “poisoning attacks” that inject malicious data into training sets to corrupt AI models. Developing resilient AI models that can withstand such attacks is an ongoing area of research and development.
Data Quality and Bias
The effectiveness of any AI system is heavily dependent on the quality and diversity of its training data. Biased or incomplete datasets can lead to AI models that misidentify threats, generate false positives, or even overlook certain types of attacks. Ensuring the integrity and representativeness of training data is paramount.
Complexity and Explainability
Many advanced AI models, particularly deep learning networks, operate as “black boxes,” making it difficult to understand how they arrive at their decisions. In cybersecurity, where every alert can have significant implications, the ability to explain an AI’s reasoning (explainable AI or XAI) is crucial for trust, auditing, and compliance.
Resource Intensity
Training and deploying sophisticated AI models require substantial computational power and large datasets. This can be a barrier for smaller organizations with limited resources, though the rise of cloud-based AI security solutions is helping to democratize access.
Ethical Implications
The use of AI in monitoring and defense raises ethical questions regarding privacy, surveillance, and the potential for misuse. Striking a balance between robust security and individual freedoms is a complex challenge that requires careful consideration and robust regulatory frameworks. AI compliance management becomes critical here, ensuring AI systems adhere to data protection regulations like GDPR and CCPA.
The Future of Cybersecurity AI: Trends and Innovations
The journey of AI in cybersecurity is just beginning. Several key trends are shaping its evolution:
Hyper-Automation and Self-Healing Networks
The vision of truly AI security automation extends to self-healing networks that can not only detect and respond to threats but also automatically reconfigure themselves, patch vulnerabilities, and restore compromised services with minimal human intervention.
Contextual AI and Autonomous Systems
Future AI systems will possess even greater contextual awareness, understanding the nuances of user roles, business processes, and external events. This will lead to more intelligent and autonomous security decision-making, moving towards a truly proactive cyber defense.
Quantum-Resistant AI
As quantum computing emerges, the threat to current encryption standards will necessitate the development of quantum-resistant cryptographic solutions. AI will play a role in both developing and protecting these next-generation security protocols.
Edge AI for IoT Security
With the proliferation of IoT devices, securing the “edge” becomes critical. Lightweight AI models deployed directly on IoT devices can provide immediate, localized threat detection and response, minimizing latency and improving overall security posture.
AI for Supply Chain Security
The increasing complexity of global supply chains makes them attractive targets for cyber attackers. AI will be crucial in monitoring and securing these intricate networks, identifying anomalies in software components, hardware, and operational processes to prevent large-scale compromises.
[Related: sustainable-tech-innovations-greener-gadgets-eco-smart-living/]
Conclusion
The integration of AI in cybersecurity is no longer a futuristic concept; it is a present-day imperative. From enhancing AI threat detection capabilities to enabling automated threat response and predictive cybersecurity AI, artificial intelligence is fundamentally reshaping our approach to digital defense. It empowers organizations to detect threats faster, respond more effectively, and proactively anticipate attacks in an increasingly hostile digital environment.
While challenges such as adversarial AI and ethical considerations remain, the continuous advancements in machine learning cybersecurity promise an even more secure future. The collaborative intelligence of humans and AI will form the bedrock of next-gen cyber defense, ensuring that our digital lives, data, and critical infrastructures are protected against the ever-evolving tactics of cyber adversaries. By embracing AI security solutions and fostering a culture of innovation, we can build a more resilient and secure digital world for everyone.
FAQs
Q1. How is AI used in cybersecurity?
AI is used in cybersecurity for various critical functions including enhanced threat detection (identifying anomalies, malware, and sophisticated attacks), automated incident response, predictive analytics to foresee vulnerabilities, and optimizing security operations through alert prioritization and root cause analysis.
Q2. What are the benefits of AI in cybersecurity?
The primary benefits of AI in cybersecurity include faster and more accurate threat detection, automated response capabilities, reduced human workload, improved predictive capabilities, enhanced anomaly detection, and the ability to process and analyze vast amounts of data more efficiently than human analysts.
Q3. Can AI replace human cybersecurity analysts?
No, AI cannot fully replace human cybersecurity analysts. AI excels at processing data, identifying patterns, and automating routine tasks, but human analysts provide critical thinking, intuition, contextual understanding, and the ability to adapt to unique and unforeseen threats. The most effective approach is a collaboration between AI and human expertise.
Q4. What is AI threat detection?
AI threat detection refers to the use of artificial intelligence and machine learning algorithms to identify and flag potential cyber threats. This involves analyzing network traffic, user behavior, and system logs to detect anomalies, known malware signatures, and novel attack patterns that might indicate a breach or malicious activity.
Q5. How does machine learning improve cybersecurity?
Machine learning improves cybersecurity by enabling systems to learn from data without explicit programming. It allows for the detection of unknown threats (zero-days), improves fraud detection accuracy, enhances vulnerability management by predicting attack likelihood, and automates many aspects of security analysis and response.
Q6. What are some examples of AI security solutions?
Examples of AI security solutions include AI-powered endpoint detection and response (EDR) systems, AI-driven Security Information and Event Management (SIEM) platforms, AI-based fraud detection systems in finance, AI for cloud security posture management, and intelligent systems for email phishing detection.
Q7. What is the future of AI in cybersecurity?
The future of AI in cybersecurity involves greater hyper-automation, more sophisticated predictive capabilities, self-healing networks, and increasingly autonomous security systems. We can also expect advancements in quantum-resistant AI, edge AI for IoT security, and enhanced AI for supply chain protection, all while addressing ethical considerations and adversarial AI challenges.